Digital License Plates Could Be Used to Track You, Steal Data, Hackers Find
Adding a permanent, connected device to your car might have some upsides. It also introduces a new way for hackers to track you or collect personal information, as first reported by Vice.A group of cybersecurity researchers recently published a report on various weaknesses they’ve discovered in connected cars. The hackers found ways to precisely locate cars from major OEMs, including customer names, phone numbers, email addresses, and loan statuses.
For Reviver’s RPlates, the hackers discovered they could change the message the plates displayed and, yes, track the cars. The vulnerability has been fixed.
UPDATE 1/12/2023: The California DMV told Car and Driver, in response to our query, that the digital plates are currently at the pilot stage, but added: “The DMV is currently developing regulations to implement the permanent program. Privacy and security standards will be addressed in the regulations, including requiring the digital plate system or any other approved device to meet or exceed minimum national security standards.
“Digital license plates offered in the current pilot are not connected to DMV systems, and therefore DMV systems are not at risk through this program. Reports of the security and privacy issues are deeply concerning, and the DMV is in contact with Reviver to gain assurances the actions they have taken since this situation occurred have indeed corrected the issue.”
Well, that didn’t take long. The California DMV approved new digital license plates from Reviver in October, and now we’ve learned how vulnerable they could be to outside hacking attacks.
One More Thing That’s Digital
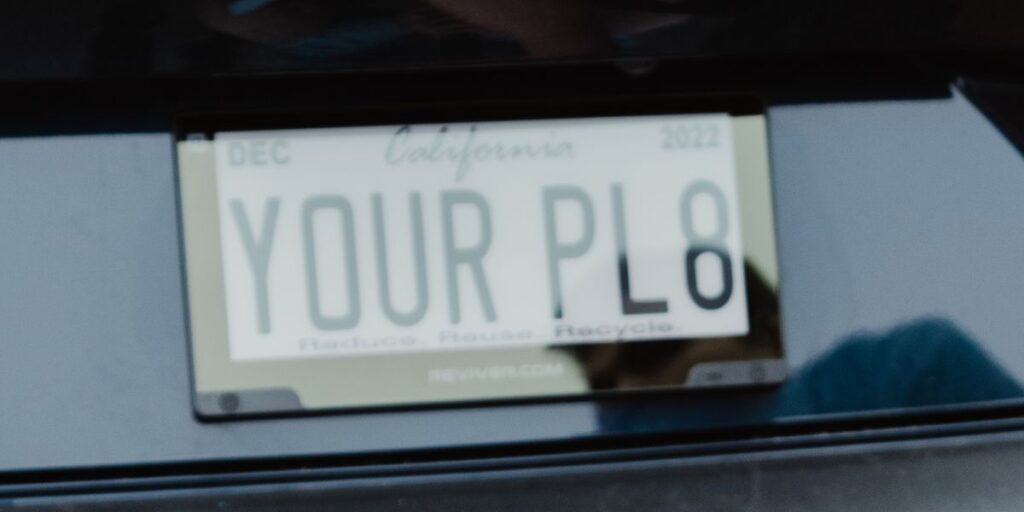
Reviver, the only company that offers digital license plates, points out that they provide some technical benefits over traditional metal plates, like automatic tag renewals and the ability to change what they say to things like STOLEN in case the car it’s attached to is, well, stolen. But there have always been downsides, including higher cost and added complexity.
Last week, as Vice reported, a group of cybersecurity researchers interested in finding access points to connected vehicles announced they had found vulnerabilities in several brands and services. This included the ability to locate and track vehicles from multiple brands, including Kia, Honda, Infiniti, Nissan, Acura, Hyundai, and Genesis. They could also find personal details on customers of many brands, including the loan status of Toyota customers, according to the published report.
When it came to a connected vehicle network called Spireon that is mainly involved with fleet-management applications, the hackers said they “had access to everything.” For Reviver, the team accessed the network without too much apparent hassle.The cybersecurity researchers published the details of how they gained access to Reviver’s back end, which involved viewing how the app and other online services behaved during a password reset request. People with more understanding of lines of code can see the details here.
Reviver
Once inside Reviver’s network, the researchers had “full super administrative access” to all user accounts and vehicles for all Reviver-connected vehicles. This would have allowed them to track the physical location of these plates, change the plate to say whatever they wanted, and access all user records, “including what vehicles people owned, their physical address, phone number, and email address.”
Officially, Reviver admits that the customer data it collects might be vulnerable to outside actors. “We have adopted reasonable and appropriate security procedures to help protect against loss, misuse, and unauthorized access to the information you provide to us,” the company said on its website. “Please note, however, that no data transmission or storage can be guaranteed to be 100% secure. As a result, while we strive to protect your information and privacy, we cannot guarantee or warrant the security of any information you disclose or transmit to the services.”
Reviver Responded Quickly
Things appear to be solved, for now. The cybersecurity researchers said they reported the vulnerability to Reviver, and it was quickly patched. Still, had these white-hat hackers not been trying to fix problems, they had the power to “remotely update, track, or delete anyone’s Reviver plate.” The researchers said they “could additionally access any dealer (e.g., Mercedes-Benz dealerships will package Reviver plates) and update the default image used by the dealer when the newly purchased vehicle still had Dealer tags.” They also gained full access to Reviver’s fleet management functionality.
In a statement, Reviver told Car and Driver it met with a member of the cybersecurity research team after being informed of the potential application vulnerability.
After the meeting, Reviver not only patched its application in under 24 hours, it also “took further measures to prevent this from occurring in the future.” Reviver said no customer information was affected. “As part of our commitment to data security and privacy, we also used this opportunity to identify and implement additional safeguards to supplement our existing, significant protections,” the company said. “Cybersecurity is central to our mission to modernize the driving experience and we will continue to work with industry-leading professionals, tools, and systems to build and monitor our secure platforms for connected vehicles.”
This content is imported from poll. You may be able to find the same content in another format, or you may be able to find more information, at their web site.



